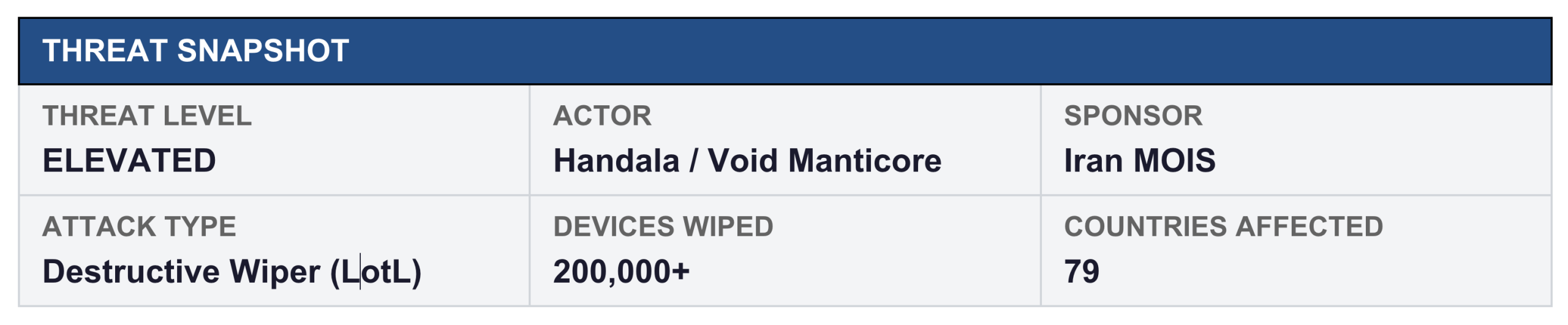
Iran’s most destructive cyber unit didn’t deploy malware to wipe 200,000 devices at a multi-billion dollar medical device manufacturer this week. They used Microsoft’s own MDM platform. The era of ‘no malware detected = no breach’ is over.
 On March 11, 2026, eleven days after U.S. and Israeli forces began Operation Epic Fury with strikes on Iranian military targets, Iran-linked hacking collective Handala executed one of the most operationally damaging cyberattacks in recent memory. The target: a $25 billion medical device manufacturer headquartered in Portage, Michigan.
On March 11, 2026, eleven days after U.S. and Israeli forces began Operation Epic Fury with strikes on Iranian military targets, Iran-linked hacking collective Handala executed one of the most operationally damaging cyberattacks in recent memory. The target: a $25 billion medical device manufacturer headquartered in Portage, Michigan.
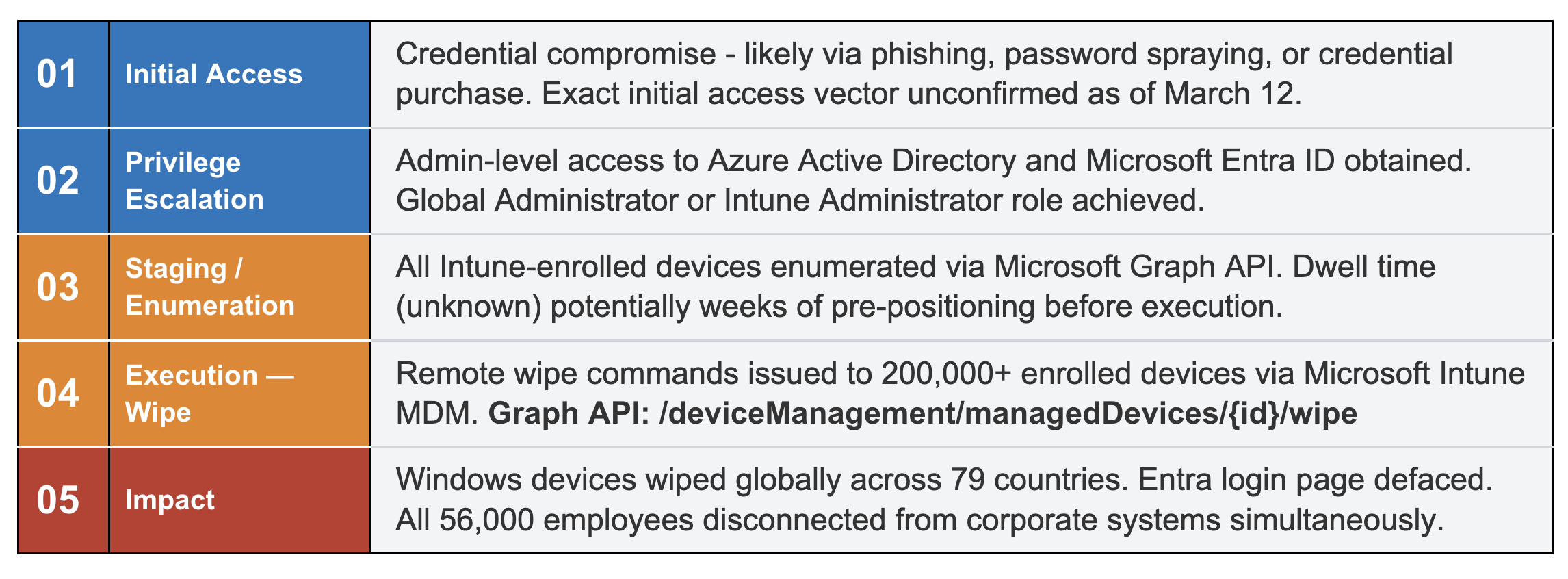
The attack was not ransomware. There were no known malicious executables used. The organization’s own security tools likely saw nothing unusual until it was too late. Handala wiped the company’s global device estate, including servers, laptops, and mobile phones, using Microsoft Intune – the same cloud-based MDM platform its IT team used for daily device management.
This is the new shape of nation-state cyber warfare: no malware, no zero-days, just stolen credentials and a few API calls.
What Happened?
The attack commenced at approximately 3:30 AM EDT on March 11, targeting a moment of minimal IT staffing. Within hours, employees across 79 countries found themselves completely locked out of corporate systems. The company’s Microsoft Entra ID login page was defaced with the Handala group’s logo.
They proceeded to file a regulatory disclosure stating the company was working to restore operations, with the timeline for full recovery unknown. The company’s stock fell approximately 3.2% on the day. Ireland’s NCSC was notified because the company’s Cork hub was among the most severely affected locations.
|
|
CRITICAL Classification Note
|
Handala claimed to have wiped more than 200,000 servers, workstations, and mobile devices — and to have exfiltrated 50 terabytes of corporate data prior to the wipe. The data exfiltration claim remains unverified. Handala’s stated motive: retaliation for the February 28 airstrike on a school in Minab, Iran, in which over 170 people were killed. The group identified the company as a ‘Zionist-rooted corporation,’ likely referencing its acquisition of an Israeli company in 2019.
The Attack Chain: How Legitimate Tools Become Weapons
This attack is a masterclass in living-off-the-land tradecraft applied at a destructive scale. Each step in the chain used legitimate Microsoft infrastructure: no custom implants, no exploit frameworks.
Key Insight
|
Who Is Handala — and Who Is Really Behind Them
Handala Hack Team emerged in late 2023 following the Hamas October 7 attacks. The group presents itself as a hacktivist collective, but Palo Alto Unit 42, IBM X-Force, and Falcon Feeds have assessed it as a front for Void Manticore, a destructive threat group directly affiliated with Iran’s Ministry of Intelligence and Security (MOIS).
Void Manticore’s defining characteristic is an ‘opportunistic and quick-and-dirty’ operational tempo focused on maximum visible damage. Their 2026 campaign has included:
- The March 11 wiper attack (200,000+ devices)
- A claimed March 11 breach of Verifone payment systems
- Doxxing of Israeli Air Force officers (50+ individuals published)
- Targeting of oil and gas infrastructure in Jordan and Saudi Arabia
- Operations routed through Starlink IP ranges (AS14593) to obscure attribution
Iran’s Broader Campaign: Multiple APT Groups Now Active
This MDM attack is one data point in a coordinated, multi-actor Iranian cyber campaign that accelerated immediately after the first U.S.-Israeli strikes on February 28.
MuddyWater (Seedworm) | MOIS-affiliated
Broadcom Symantec confirmed MuddyWater intrusions inside U.S. banks, airports, non-profits, and a defense/aerospace software company. The group deployed a new backdoor named Dindoor, built on the Deno JavaScript runtime. A second implant, Fakeset, was deployed at a U.S. airport and non-profit. Rclone was used to attempt data exfiltration to a Wasabi cloud storage bucket.
Agrius (Pink Sandstorm) | MOIS-affiliated
Agrius has been aggressively scanning internet-facing IP cameras using CVEs including CVE-2017-7921 and CVE-2023-6895. Researchers assess this as battle damage assessment (BDA) support for Iranian missile operations — surveilling strike aftermath in real time using compromised camera infrastructure across Kuwait, Jordan, and Bahrain.
Charming Kitten, OilRig, Fox Kitten | IRGC/MOIS
Signs of rapid retooling and renewed activity observed across multiple long-standing Iranian APT groups. These actors bring sustained, patient intrusion capabilities and are likely pre-positioning in enterprise environments for future operations.
Wiper Arsenal Context
|
Industry Context: The Attacker’s Playbook Has Already Shifted
This MDM attack did not happen in a vacuum. The industry’s three major 2025 threat reports all independently confirmed the same structural shift that enabled it: attackers have largely abandoned malware delivery in favor of credential theft and identity abuse.
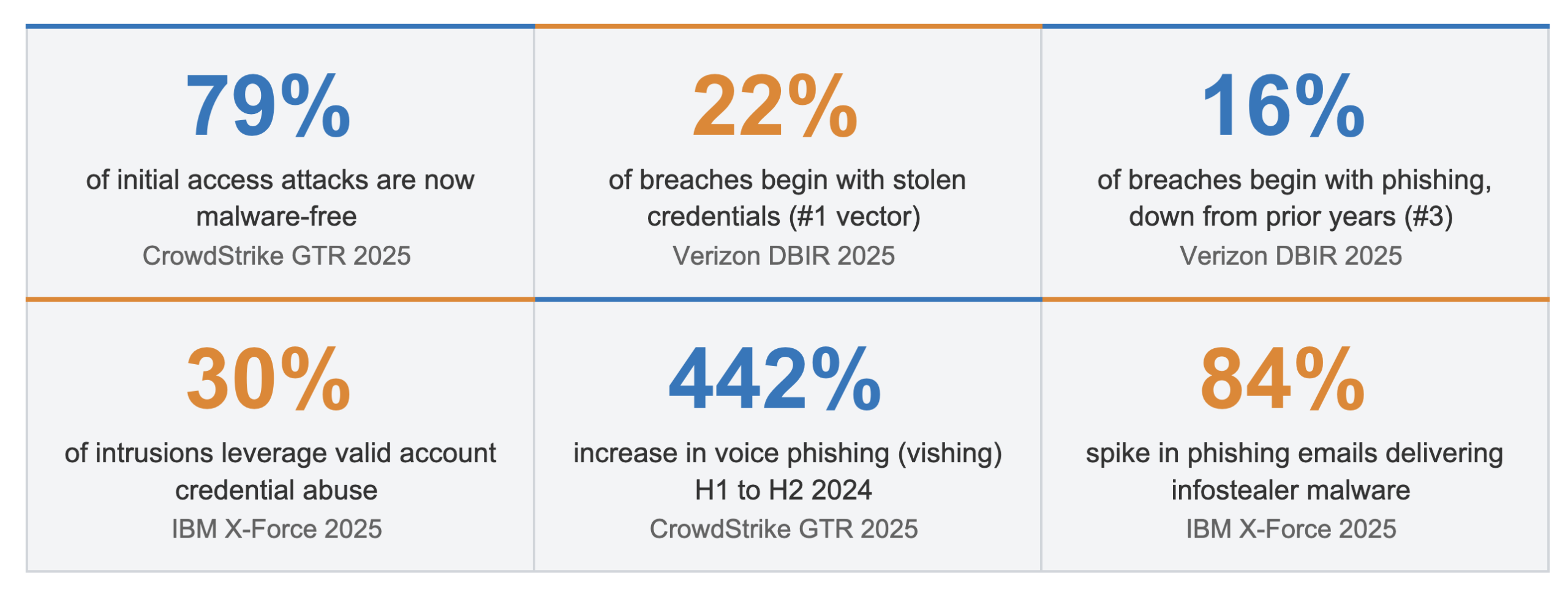
The picture is consistent: phishing is no longer primarily a direct compromise method; it has become the front end of a credential theft pipeline. When an attacker has valid admin credentials to your Intune tenant, they are your IT department.
Detection Recommendations: Where to Look When There’s No Malware
The critical principle for detecting an attack of this class is this: EDR telemetry will not catch it. No process was spawned on an endpoint. No file was written. The entire attack lived in cloud audit logs: Entra ID sign-in logs, Intune audit logs, and Azure AD activity logs. Detection must shift accordingly.
Entra ID / Identity Layer
|
Microsoft Intune / MDM
|
Active Directory
|
Behavioral / Cloud Audit
|
XDR-specific approach: Ingest Entra ID and Intune logs from Microsoft Graph API. Build an alert rule on bulk wipe events: filter Audit Logs where the Operation Name == “Wipe device” with a count threshold over a short rolling window. Baseline normal wipe volume, so your threshold is meaningful.
What to Do Right Now
Immediate Actions
- Audit all Entra ID Global Admin and Intune Administrator role assignments and remove any accounts that do not absolutely require that privilege.
- Enable Conditional Access policies that block legacy authentication and require phishing-resistant MFA (FIDO2 hardware keys) for all administrative roles. Standard TOTP-based MFA is bypassed by adversary-in-the-middle phishing kits at scale.
- Review Intune audit logs for baseline activity to understand what normal device wipe/retire volume looks like so you can alert on anomalies.
- Block or monitor Starlink IP ranges (AS14593) in Entra ID Conditional Access. Legitimate sign-ins from Starlink should be rare for enterprise accounts.
Short-Term Actions
- Implement Privileged Identity Management (PIM) for the Intune Administrator role: require just-in-time elevation with manager approval, eliminating the standing admin access that enabled this attack.
- Restrict Microsoft Graph API access to device management endpoints to named, approved service principals only. Human accounts should not have programmatic wipe capability.
- Enable Microsoft Defender for Identity (if licensed) and configure alerts for DCSync, LDAP enumeration, and Kerberoasting – the early signals of an attacker moving toward domain dominance.
- Hunt for password spray patterns in Entra sign-in logs: high count of unique usernames, low per-account failure rate designed to stay under lockout thresholds.
- Verify patch status on all internet-facing edge devices: VPN concentrators, Citrix NetScaler, Fortinet, F5 BIG-IP. Iranian actors have a documented history of exploiting CVE-2019-19781, CVE-2022-1388, and CVE-2024-23113.
A Final Note on Context
It is worth noting that CISA is currently operating at approximately 38% staffing due to federal funding constraints. No official U.S. government advisory on the attack or Intune/MDM abuse TTPs had been published as of March 12, 2026. The absence of government guidance does not mean the threat is low; it means private-sector detection and intelligence sharing is carrying more weight than usual.
Watch the following sources for emerging IOCs and updated guidance: Symantec Threat Intelligence, CrowdStrike Adversary Intelligence, Mandiant, Palo Alto Unit 42, and Ireland’s NCSC. File hashes as they are published, C2 infrastructure, and the confirmed initial access vector for this specific attack have not yet been publicly released.
The geopolitical context remains highly dynamic. If kinetic operations continue under Operation Epic Fury, Iranian cyber actors, state-directed and proxy alike, will continue to seek retaliatory targets in Western critical infrastructure, healthcare, and financial services. Any organization with Israeli business ties, supply chain relationships, or dual-listed operations should treat this threat as active and immediate.