DON’T TAKE A Chance BETTING ON SECURITY.
GO WITH A SURE THING: PRESIDIO
PRESIDIO CAN HELP YOU MIGRATE, MANAGE AND SECURE YOUR DATA IN THE CLOUD.
What is Cloud Security?
The art of protecting cloud infrastructure, workloads, and data from unauthorized access or criminal use and the practice of ensuring confidentiality, integrity, and availability of information.
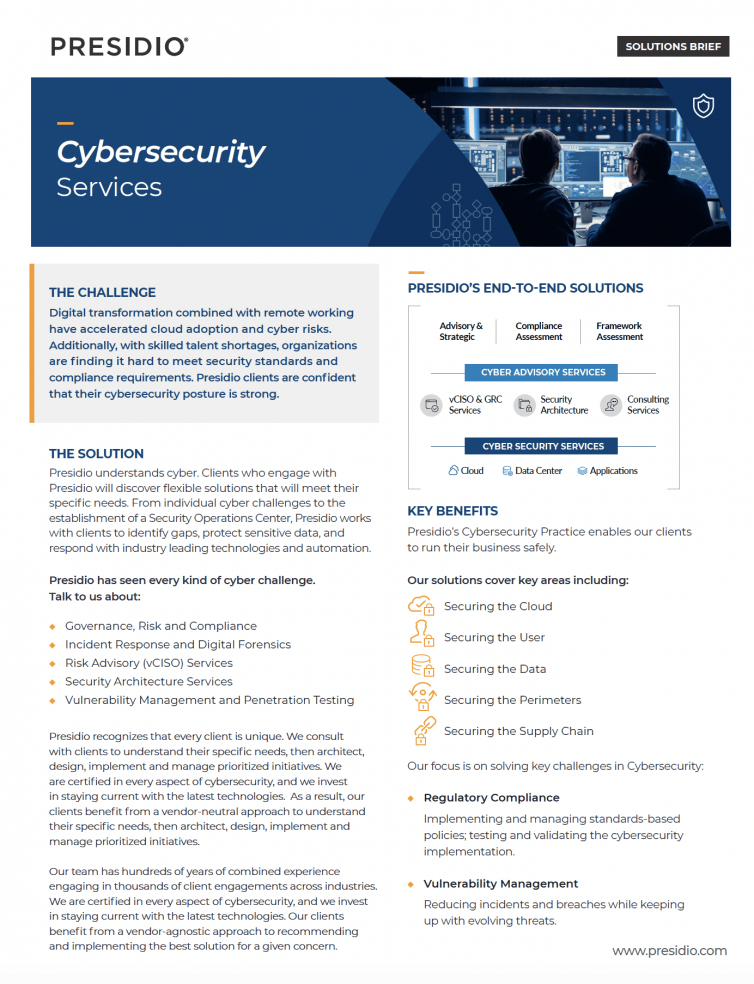
CLOUD SECURITY AT PRESIDIO
Presidio’s vast experience with cloud migration and development, combined with award winning security expertise, enables us to offer customized cloud security solutions for customers of all sizes and verticals.
*Systems Integrators lack true Cyber Security expertise
*Cyber Providers lack expertise in full lifecycle IT services
*Born in the Cloud providers lack abilities in both
PRESIDIO = MATURITY, BREADTH, DEPTH

CUSTOMERS WE CAN HELP. ARE YOU…
- Starting out?
Presidio helps customers as they begin their journey to the cloud. By prioritizing cybersecurity with the move to cloud, customers can save time, money and stress in the future. - Already in the cloud?
Although the best time to look at cloud security is during the initial move to cloud, it’s never too late to review your cloud security posture and make improvements. - Hybrid Cloud?
Presidio brings in traditional security frameworks that apply to both on-prem and cloud environments. - Healthcare and Financial industries?
Presidio provides the insights needed into compliance and governance of data in the cloud. - SLED?
Presidio has a dedicated team of SLED focused practitioners, experts and CISO that understand the specific needs of State and Local Governments and Educational Institutes.
UPCOMING EVENTS
Events
Get the details on upcoming events and offerings to Win the Race to Cloud Security
CLOUD SECURITY RESOURCES
BLOGS
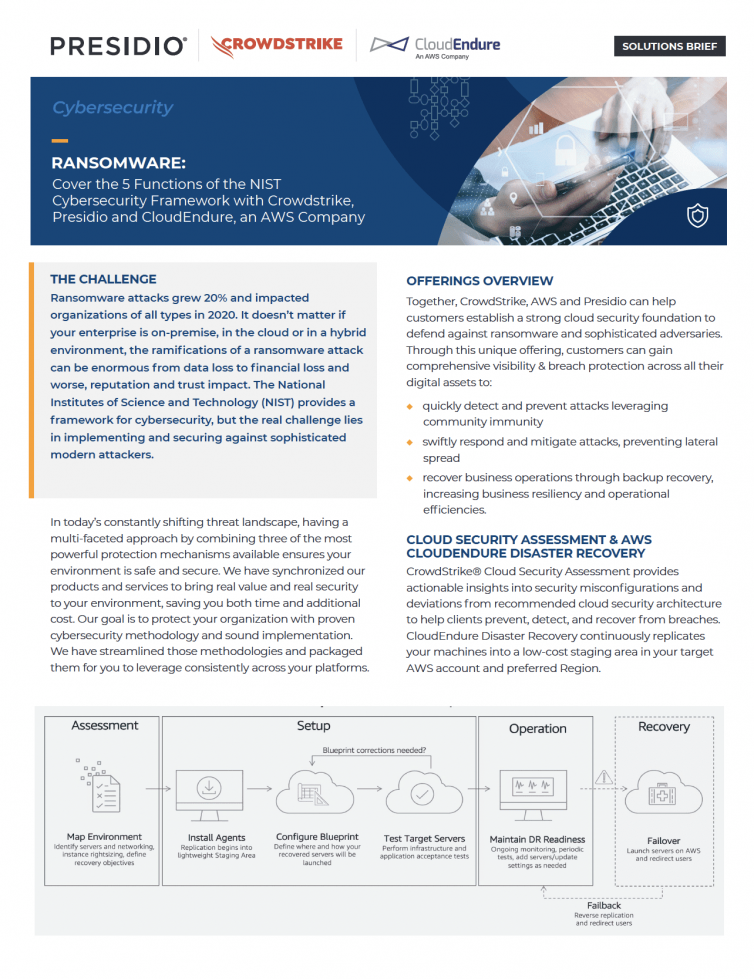
These security missteps represent common low-hanging fruit attackers seek to infect companies with ransomware and other costly exploits. Before the pandemic, cloud adoption was already expanding rapidly, and it accelerated even faster once companies had to make urgent changes to their business operations. For example, the Flexera 2021 State of the Cloud Report found that 61% of companies made slightly higher-than-planned cloud investments and 29% made significantly higher-than-planned cloud investments in 2020. However, besides the overnight changes in how companies work, another area witnessed explosive growth: cyberattacks. According to a research study by Deep Instinct, ransomware attacks increased 435% in 2020 compared with 2019, and malware increased 358% during the same period. Additionally, the average ransomware payout has grown to nearly $234,000 per event, according to cybersecurity firm Coveware.
The value of the public cloud and the benefits it provides are evidenced by its aggressive growth and wide acceptance. To support the continued strength of public cloud as an essential element in a modern data center solution, Presidio has emphasized the importance of a robust and optimized infrastructure, taking a methodical approach to identifying which instances are most appropriate for any given workload.
Many companies are migrating to the cloud, but they have to navigate various complexities and avoid a few “gotchas” along the way. The “work from anywhere” trend accelerated by the pandemic last year has become the new norm for many businesses, and it’s leading to an explosion of cloud adoption. Analysts estimate that 90% of enterprise customers are looking to the cloud for calling and other unified communications (UC) infrastructure. There are undeniable benefits of migrating calling and collaboration to the cloud, but you’re missing out if you’re not integrating these solutions and other business apps. Consider the following example: A collaboration team works in the same document via a file-sharing application, and they want to update other contributors. The app sends notices via email and connects with calling, messaging and meeting apps from three vendors. Each contributor is forced into an endless cycle of context switching between three or more applications while actively collaborating on the project. Sadly, this is the norm for many companies.
As a fast, easy alternative for compute and storage resources, the public cloud practically sells itself: it requires no large up-front capital expenditures, its pay-per-usage model delivers the speed and agility to get to market fast, and it’s ideal for hosting short-term or trial content. What’s more, leading cloud environments are optimized for reliable performance on Intel® technology for the data center.
SPONSORING PARTNERS
CONTACT US NOW TO WIN THE RACE TO CLOUD SECURITY!
Please fill out the form below or contact us on social media.