Forecasts are baked into our daily lives. From tomorrow’s weather to this Sunday’s games, experts make predictions all the time. But in the cybersecurity world, predictions hold a little more weight.
Experts around the globe compile and analyze extensive data to reveal exactly what happened in the previous year and predict the trouble to come.
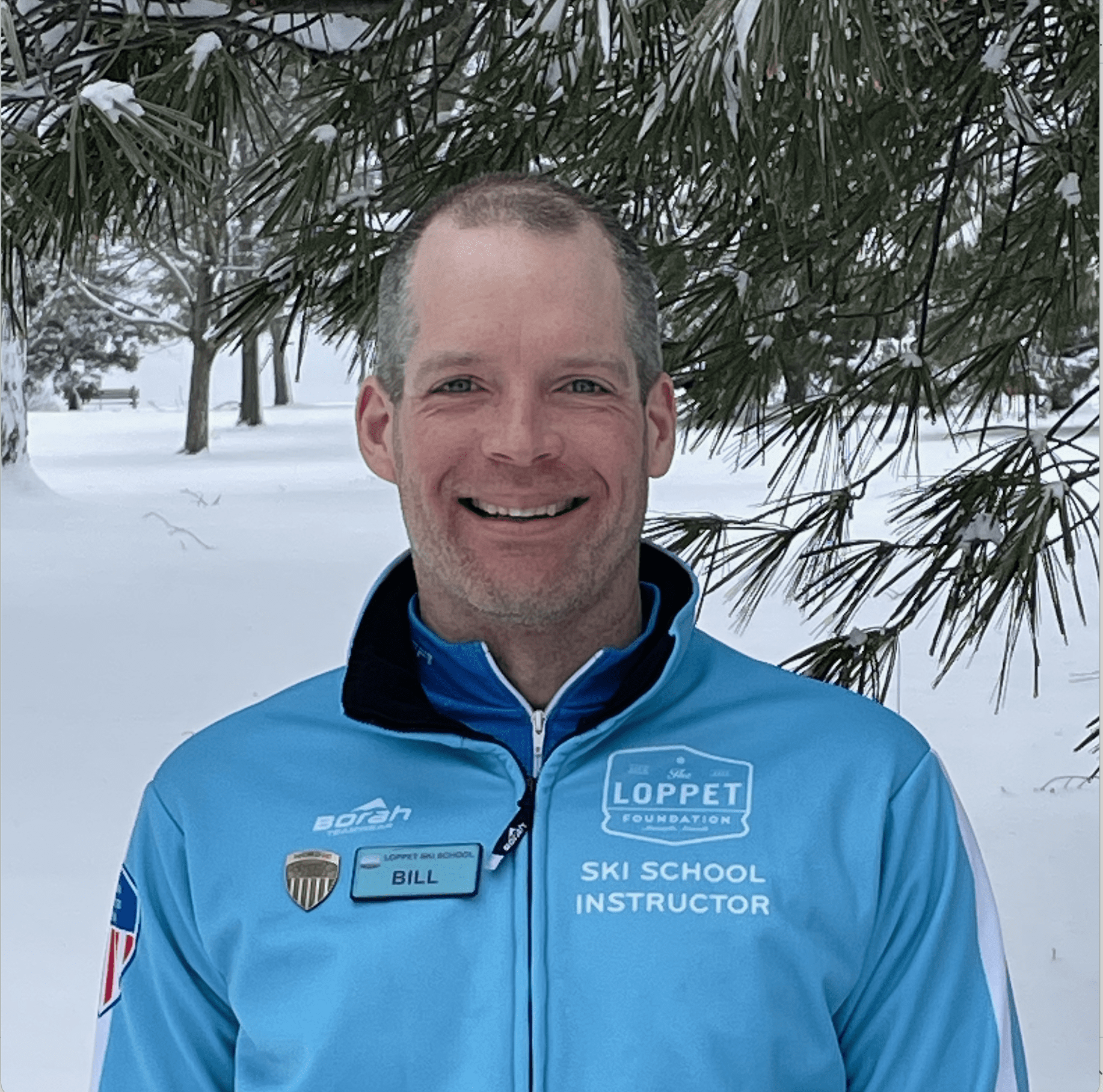
In the most recent episode of The Digital Decode, Dave Trader and Dan Lohrmann, both Field CISOs at Presidio, discuss precisely what will take the stage in 2023 and why you can’t afford to ignore these data-based predictions.
Join us as we discuss:
- A recession in cyber talent
- Cybercrime and insurance
- Hacktivism and foreign threats
High competition, low headcount: A look at where cyber talent is going
For years, there has been a shortage of skilled professionals in the cybersecurity space. While that trend is likely to continue, there will also be a shift in where these security professionals are concentrated.
Instead of companies competing for a limited number of experts, there will be a greater focus on outsourcing cybersecurity needs. This means that there will be a shift in which cybersecurity professionals will begin to work in separate entities, serving in more of a contractor position.
“Unless your primary business is cybersecurity, you’re not going to have those people on staff anymore,” says Dave. “This will let businesses get back to their core function.”
While there are many benefits to shifting towards hiring cybersecurity professionals through a contractor approach, this will also mean that the competition for the best of the best will be fiercer.
While talent was once limited to geographic location, most professionals now have the ability to clock in and perform their duties from anywhere — which means any business can hire top talent from anywhere around the globe.
Changes in cyber insurance and why you may now be denied coverage
Insurance has always been a vital part of cybersecurity, but this sector has previously failed to truly understand how cyber truly functions. After hard lessons learned regarding the Ukraine war, cyber insurance companies are leveling up and investing in understanding every principle required to maintain security.
While various controls are required for different sectors — cybersecurity will, of course, look different in healthcare than it does in banking — insurance providers are creating systems that require proof of specific controls.
Businesses will no longer be allowed to provide self-attestation regarding their security protections. Instead, insurance companies will likely begin to require third-party certificates and validation for established controls before issuing insurance, even if you’ve previously been covered.
Hacktivism and foreign threats — An urge to identify the flag behind the attack
The events surrounding the Ukraine war have left a lot of people on edge wondering when the next breach will occur and who will be the target.
While foreign attacks are expected to continue to rise, another common theme will likely join — foreign attacks under the guise of another state actor.
“Watch out for false flags. When there is a global crisis, especially a war, there’s an opportunity for other nations to showcase their prowess under a false flag,” says David.
When it comes to foreign threats and attacks, allegations can escalate rapidly. Especially in the volatile environment of international relations, where it’s going to be paramount to ensure that the sources of threats and attacks are confirmed before ill-informed allegations get made.
Likewise, many reports have revealed that hacktivism will be much more prevalent in the coming years. With it will come greater challenges in multi-factor authentication and new, blended versions of ransomware.
While these many warnings can seem overwhelming and foreboding, they offer an opportunity to prepare your business and security strategy to protect yourself from impending threats.
“When you’re prepared and can get best practice in place, you are really identifying 99.9% of the risk,” Dan says. “And if you’ve done that, attackers will move on to the path of least resistance — to an easier target.”
To hear this interview and many more like it, subscribe on Apple Podcasts, Spotify, or our website or search for The Digital Decode in your favorite podcast player.
To learn more about these predictions, visit the following links:
https://www.govtech.com/blogs/lohrmann-on-cybersecurity/the-top-23-security-predictions-for-2023-part-1 https://www.govtech.com/blogs/lohrmann-on-cybersecurity/the-top-23-security-predictions-for-2023-part-2