The United States Cybersecurity & Infrastructure Security Agency (CISA) is implementing a series of regulations regarding asset vulnerability and scanning to advance its leadership within the cybersecurity landscape.
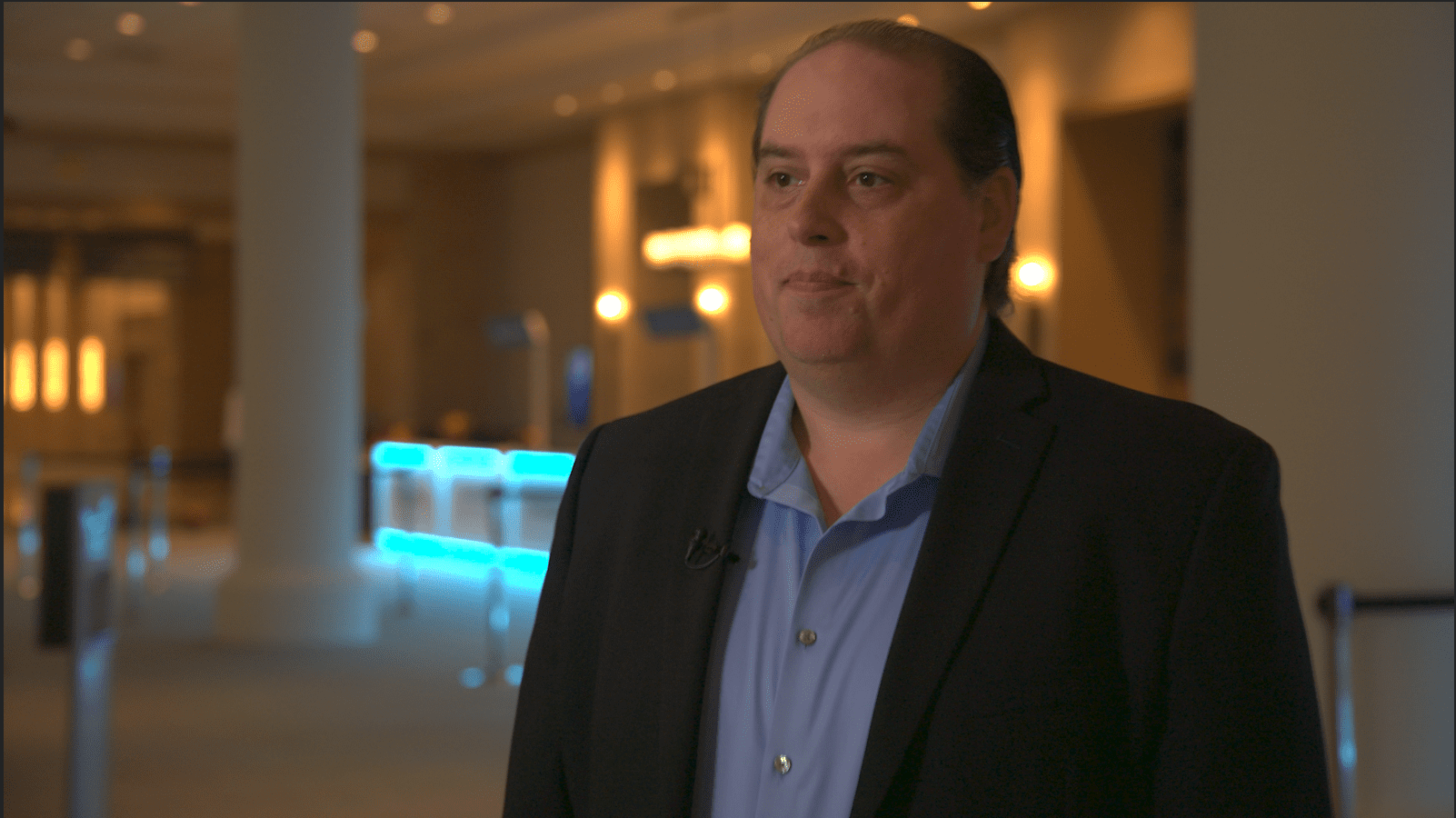
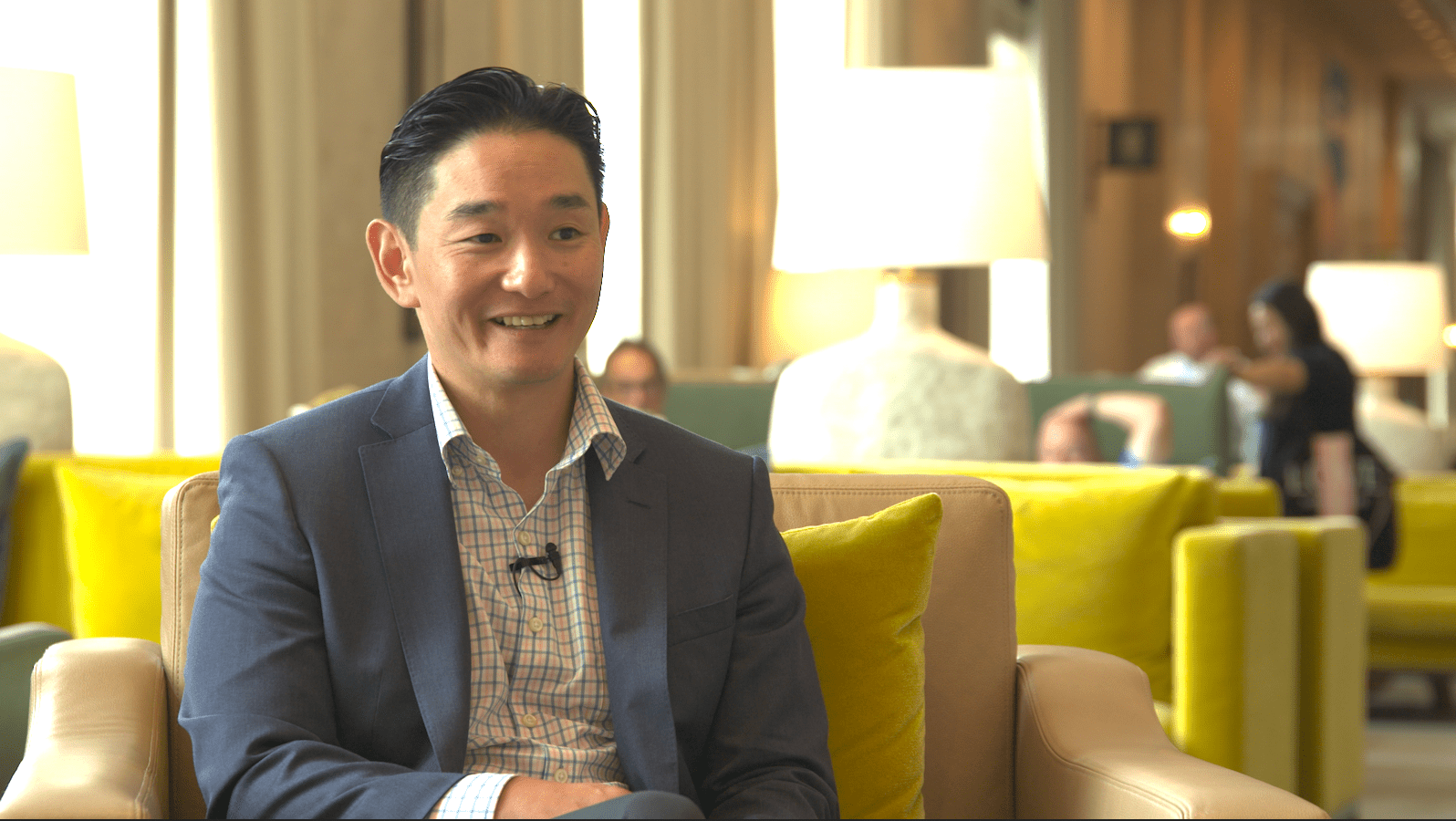
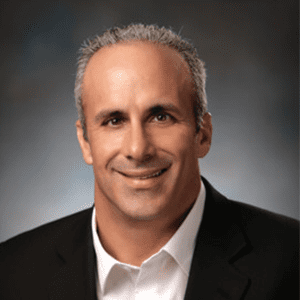
In this episode, Andy Richter, Senior Solutions Architect, Distinguished Engineer at Presidio, joins Dan Lohrmann in a conversation to close out Cybersecurity Awareness month by discussing how this federal mandate affects actors in the private sector and local and state governments.
Join us as we discuss:
- What these mandates entail
- Effects across federal, state and local governments
- Predictions for private sectors
LISTEN TO THE FULL PODCAST HERE.
Asset vulnerability and scanning regulations and what they mean
Whenever CISA pushes through new regulations, there is often talk regarding whether the efforts will positively or negatively impact federal programs and whether they will trickle down to local and state governments.
According to Andy, the most recent regulations (which will be enforced beginning April 3rd, 2023), will be excellent for cybersecurity across all sectors and levels of government.
But what exactly do these new regulations entail?
In short — automated asset discovery and vulnerability scanning.
Federal agencies will now be required to audit the discovery of every device with an IP address on their network every two weeks. This will include all devices that are IPv4 or IPv6. They must also innumerate every vulnerability that is discoverable in their networks on the same cycle.
Each of these scans must be automated and include mobile devices and roaming devices such as phones and laptops.
“This is not just your critical systems in the data centers,” Andy says. “It’s pretty much the entire enterprise.”
While initiating this effort may seem like a lift for many, there are several federal programs, large enterprises and banks that already utilize scanning systems in their cybersecurity measures that satisfy these requirements.
Overall, according to Andy, these regulations are a very positive thing, and he expects that they will be regarded as such by most.
“Applying security patches is part of any really good cybersecurity program. So requiring and normalizing the pace of scanning for these federal agencies is good.” — Andy Richter
Having been discussed, analyzed and mapped by CISA, leaders in cybersecurity have confirmed that these regulations are the best, most efficient way to ensure federal cybersecurity. While the most immediate impact of the regulations will occur on federal systems, they will also likely impact state and local governments.
Implications for federal, state, and local governments
According to Andy, It’s a good idea to adhere to the new regulations even though they aren’t currently enforced on local or state levels. But while there are many benefits, Andy predicts there will be some hesitancy on the state and local levels.
Local and state governments may jump on board with automated asset discovery and vulnerability scanning to get federal funding. However, this means there would be some level of federal monitoring of their systems.
“Sometimes there’s some tension between local, state and federal governments,” Andy says. “But the benefits outweigh the power struggle behind the hesitancy, even without grant funds.”
“The federal government and all of the tools and techniques we have in our intelligence community — the threat information the federal government gets themselves through Private Partnerships — really do know where the weak spots are.” — Andy Richter
Ultimately, these regulations have been developed with safety and security as the focus. Asset discovery and vulnerability scanning should be common practice across any organization or government, and it should occur regularly, Andy says.
Predictions for private sectors
Currently, CISA’s new regulations are not set to influence the private sector directly. Private organizations will not have to commit to regular automated scanning and discovery. While Andy does not think that all private organizations will follow new guidelines, he does think that many within the private sector will follow CISA’s suggestions — starting with insurance agencies and mid-to-large enterprises.
“If you’re not doing vulnerability management or scanning every two weeks, and you aspire to do it more frequently than you are, these are manageable challenges. It should not be cost-prohibitive for anyone.” — Andy Richter
For security experts and organizations, Andy suggests following cadence with these regulations.
“Follow the government’s leadership when helping customers decide how often to do scanning,” he says. “The federal government really does know where the weak spots are. This is what gives the biggest bang for your buck against adversaries.”
To hear this interview and many more like it, listen on Sounder, Apple Podcasts, Spotify, or our website or search for The Digital Decode in your favorite podcast player.