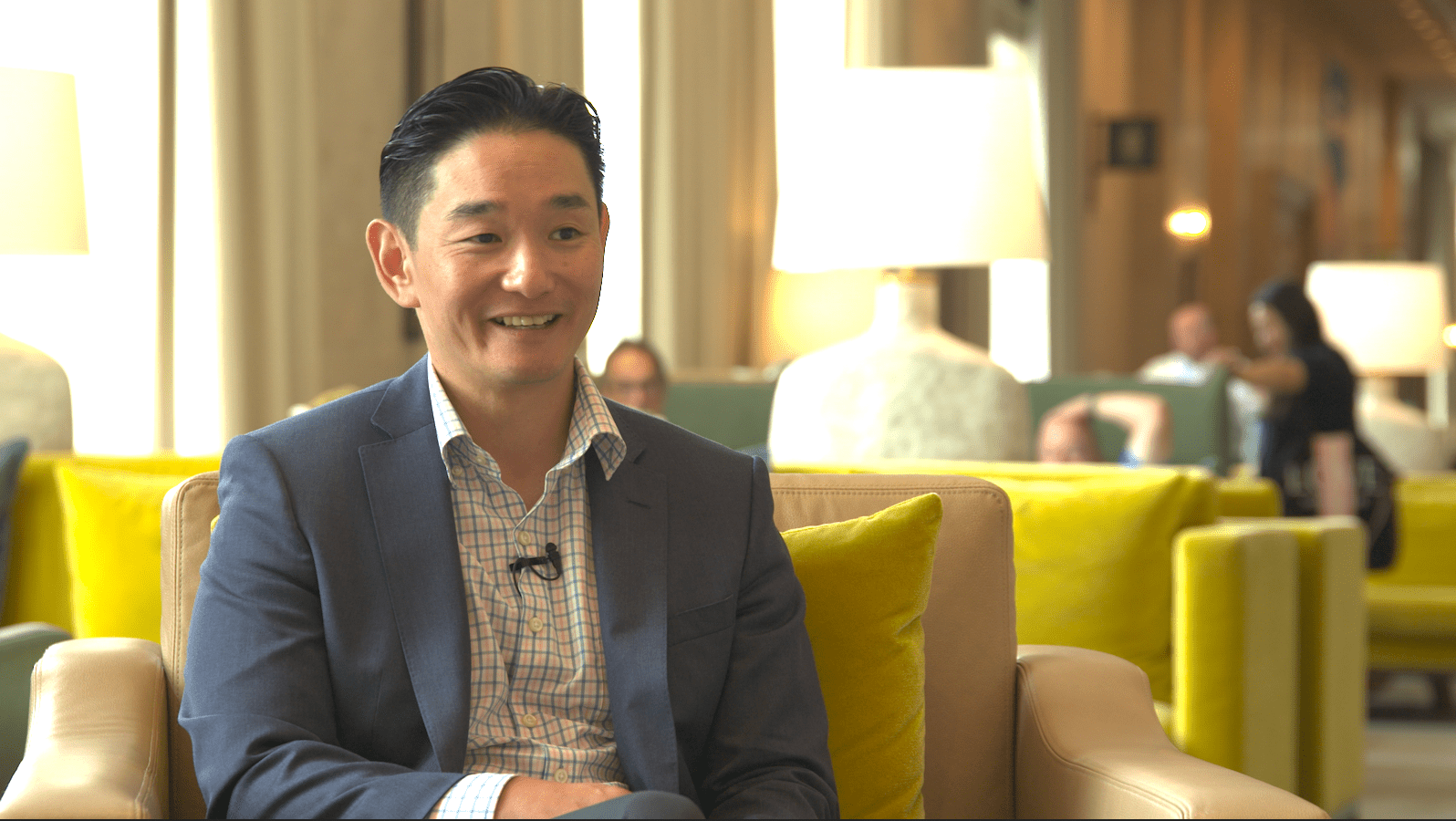
Vinu Thomas has served as Chief Technology Officer of Presidio since early 2016. He is responsible for guiding Presidio’s technology strategy, solution and services offerings and industry thought leadership. In addition, Vinu is also responsible for marketing, vendor and product management.
Vinu has built Presidio’s technology teams around networking, mobility, data center and collaboration, while also working on strategic initiatives and investments that include cloud, cyber security, data analytics and virtual desktop infrastructure.
Vinu sits on a number of advisory boards of companies like Cisco, Dell, Palo Alto Networks, Nutanix and VMWARE. Vinu is an advisory board member at Rutgers University where he serves at the Center of Innovation Education.
He was previously Vice President of Solutions for Presidio’s Tristate Area and has a total of 20 years of experience in systems integration, practice building and engineering. Prior to Presidio, Vinu led the Engineering organization for Bluewater Communications Group until it was acquired by Presidio in 2012.